Where security is not an option: defense, health, transportation, critical infrastructure
Cybersagacity’s view of Zero Trust
- Do not rely on networks to block intrusions
- Remove all mission-critical defects from critical infrastructure software
How do you know you have fixed everything that is critical?
Mission critical defects:
- Defined by expected consequence or attack types (e.g., DoS, Data Loss, Unauthorized Access)
- Never defined by AppSec severity levels
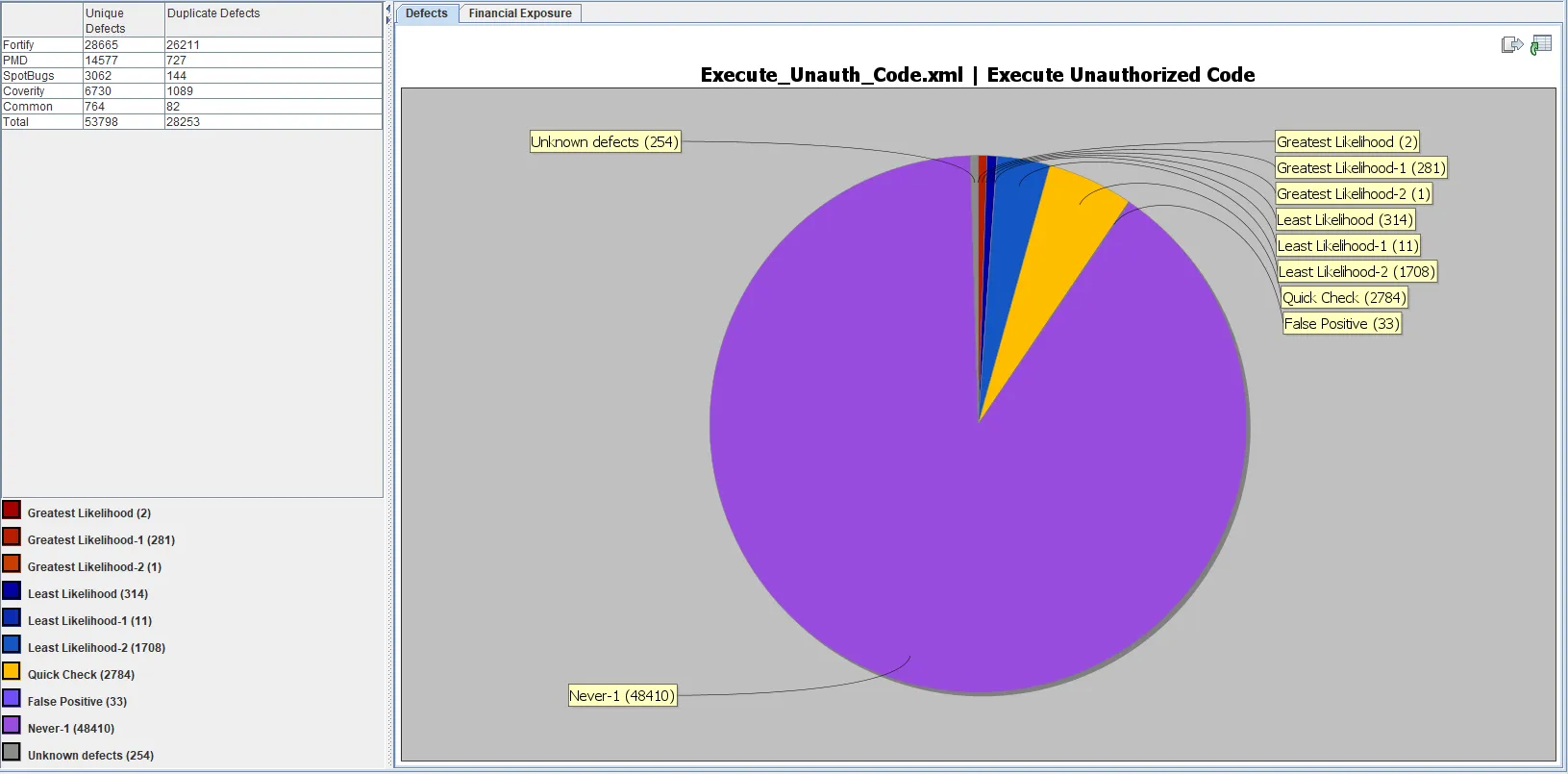
Using ASTs to find defects is a start, but which defects cause critical issues that you need to resolve? Today, the only approach would be to fix all defects – a costly, overly burdensome approach. SATriage is the only tool that not only informs the user of all possible consequences of each defect, but also ranks them by their likelihood to happen in the field.
Examples of SATriage include finding all defects with certain consequences:
- All defects that allow others to take control of a system
- All defects that allow denial of service
- All defects that allow exposure of critical data
Ranking defects 1-to-N by likelihood of occurrence allows the most rapid resolution of the most serious mission critical defects. The likelihood is a combination of the consequence probability and the chance of its exploit.
Key AppSec requirements for Zero Trust not currently considered by AppSec tools:
- Determine all consequences and attacks for every defect
- Determine coverage and accuracy of all zero trust issues found by AST vendors
- Quantify and rank defects based on zero trust properties, such as consequence and attack types