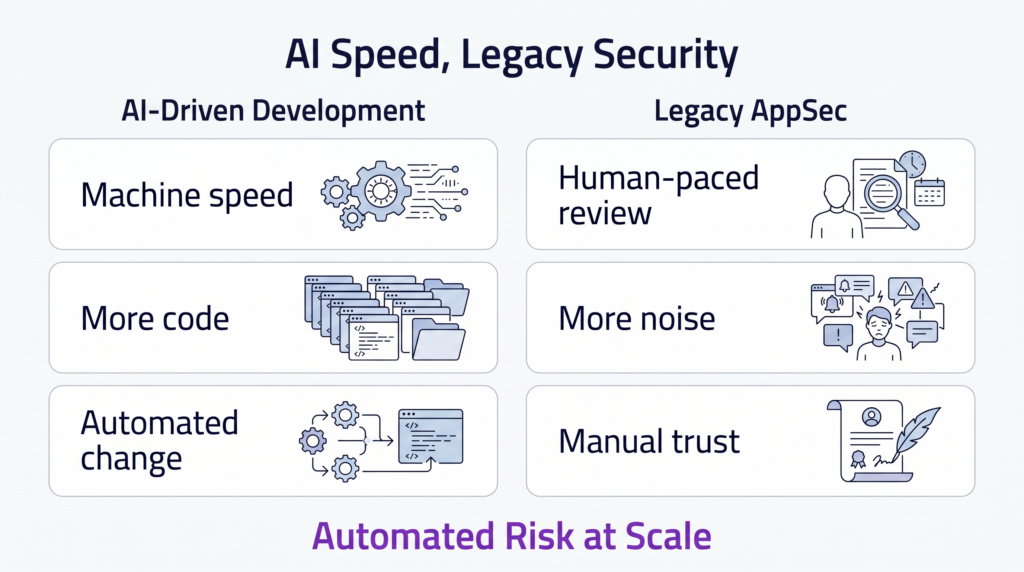
Software development has reached warp speed. With AI-driven tools now generating significant portions of new code, the dream of “assembling” software at machine speed is a reality. But for CTOs, CISOs, and engineering leaders, this revolution comes with a hidden cost: automated risk at scale.
While AI-assisted development is a profound productivity shift, it introduces structural challenges that traditional security models—designed for human-paced change and accountability—simply cannot handle.
This structural shift is already being recognized as a critical industry pivot. In fact, Bessemer Venture Partners (BVP) highlights securing AI agents as the defining cybersecurity challenge of 2026, marking a transition toward an agentic workforce that requires a fundamentally different approach to security and control.
The Reality Check: “Security Theatre” vs. Actual Assurance
Most organizations respond to this new velocity by adding more tools, yet they remain stuck in what we call “Application Security Theatre”. You might have the latest scanners, but they often create more problems than they solve:
- The Signal Collapse: Traditional tools like SAST, DAST, and SCA produce orders of magnitude more findings, but ~80% of these defects are misclassified.
- The Context Gap: AI-generated code often “looks right,” leading developers to skip deep logic reviews or contextual risk modeling.
- Wasted Engineering Cycles: Conflicting results from siloed tools lead to “alert fatigue” and a total breakdown of trust between security and development teams.
- Invisible Open-Source Risks: With open-source software (OSS) constituting 80-95% of modern apps, vulnerabilities buried in deep transitive chains often go completely undetected by standard scans.
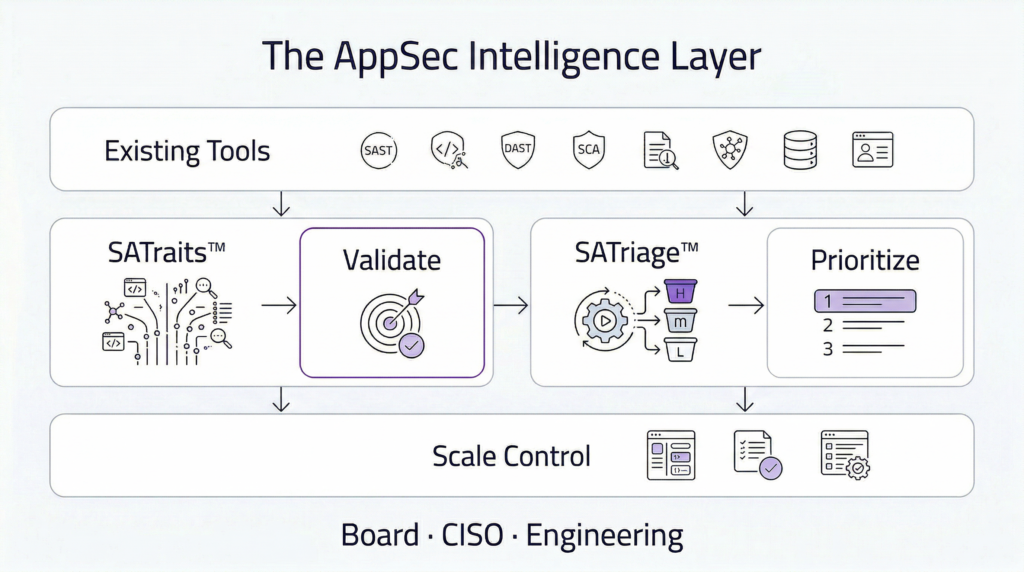
Introducing the Application Security Intelligence Layer (ASIL)
To scale safely, organizations must move beyond episodic detection toward continuous, correlated, and contextual verification. CyberSagacity delivers this missing layer, acting as a control plane that sits above your existing detection tools to provide validated risk intelligence.
1. SATraits™: Eliminating the Noise
Instead of treating every tool output as truth, SATraits evaluates the accuracy and reliability of AppSec findings.
- It integrates signals from SAST, DAST, IAST, PenTest, cloud posture management tools, and SBOMs.
- It uses decades of empirical data to statistically identify false positives and true coverage gaps.
- The result is a single, authoritative view that removes duplicates and contradictions.
2. SATriage™: Prioritization That Makes Business Sense
Not all vulnerabilities matter to your operations or your board. SATriage ranks issues by actual exploitability and material impact.
- Financial Quantification: Every defect is mapped to its expected financial loss.
- Regulatory Alignment: Findings are automatically tied to technical controls for frameworks like DORA, PCI, HIPAA, GDPR, and CMMC.
- Developer-Ready Fixes: Instead of vague alerts, developers get specific fix instructions and safe upgrade paths directly in the CI/CD pipeline.
The Outcome: Defensible Governance and Secure Velocity
The goal of modern AppSec isn’t just “more security”—it’s better decision-making. By transforming fragmented telemetry into actionable intelligence, CyberSagacity enables:
- For the Board and CFO: Business context; quantifiable risk reduction tied to financial impact and audit-ready governance for insurers and regulators.
- For the CISO: Clear prioritization of material risk and defensible evidence of “reasonable care”.
- For Engineering: Faster release cycles with fewer interruptions and a significant reduction in time spent chasing false positives.
Don’t let your development velocity outpace your control. In a world of machine-written software, you need machine-speed intelligence to stay secure.
Are you ready to stop scaling noise and start scaling control?


